Accsense
How to Connect a Cellular Modem to Your Accsense Pod
For A2-05 Ethernet Loggers and Wireless Pods via B1-06 Gateways Accsense monitoring pods use an Internet connection to monitor a wide range of physical values including Temperature, Humidity, Current/Voltage and more. However if you don’t have access to Ethernet, and you still need Accsense alarm capabilities, you can connect a cellular modem to your Accsense … Continued
Troubleshooting Extreme Temperature Readings with Accsense Installation
For the Accsense A2-05 Wired LAN Pod upon Initial Installation If you’re seeing extreme temperature readings using the Accsense A2-05 Temperature Data Logger, this problem can be diagnosed and resolved relatively quickly. Although rare, this issue causes users to see high-temperature readings in the range of 240°C, and usually indicates a broken wire, not that … Continued
Best Practices Using Your Accsense Monitoring and Alarming Data Loggers
Using your Accsense real-time monitoring and alarm system, it’s easy to access your critical data remotely from our cloud servers. To make it even easier, the Applications Specialists at CAS DataLoggers have put together a brief guide to show you how to download and archive your data from our Accsense servers for data organization and … Continued
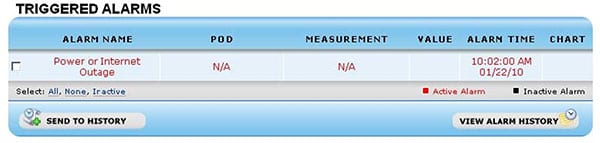
Gateway Power or Internet Outage Alerts using Accsense Data Loggers
Continual Monitoring and Alarming Systems for Healthcare and Industry CAS DataLoggers provides its Accsense wired and wireless monitoring systems to a wide variety of industries including healthcare, the life sciences, and bloodbanks. Using the standard Accsense service level which supports alarm capabilities, you can depend on your system’s default behavior to reliably respond to gateway … Continued
7 Steps to Change Communication Channels on Your Wireless Accsense System
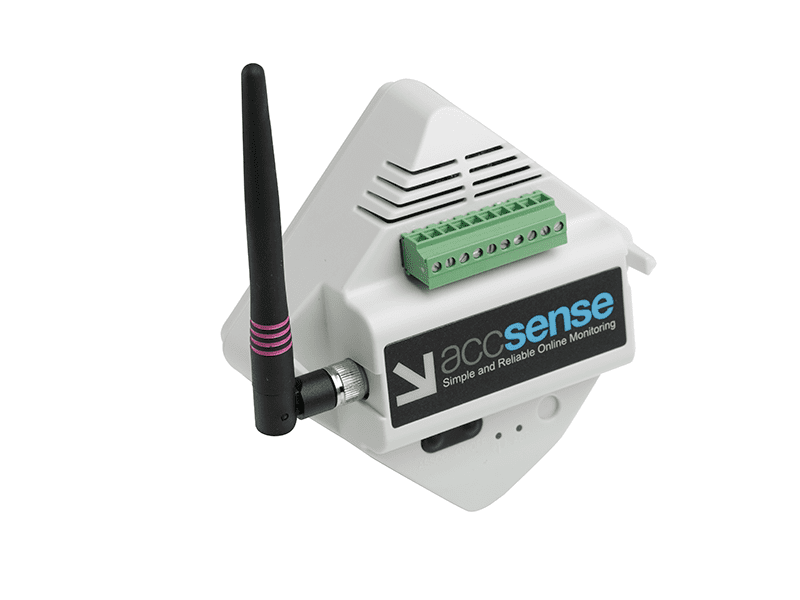
Accsense Monitoring and Alarming Systems are commonly used in hospitals, pharmacies and businesses to protect their temperature-sensitive supplies and products. Infrequently, facilities have an issue with interference caused by their own equipment such as walkie-talkies, in-hospital communications systems, and cordless phones. For these customers, the Applications Specialists at CAS DataLoggers have put together this quick … Continued
3 Ways to Troubleshoot RTD Probes on an Accsense System
Wireless Temperature Monitoring and Alarm Systems Several Accsense data logger pods can connect with PT-100 RTD temperature probes to provide highly accurate measurements. These probes are 3-wire probes and can present some problems when users do the initial install. With this in mind, the Applications Specialists at CAS DataLoggers have prepared this quick list of … Continued
3 Steps to Connect and Properly Scale a 0-5V Signal to an A1-09 Accsense Pod
Completely Automated Wireless Monitoring and Archiving Many CAS DataLoggers customers utilize Accsense A1-09 Wireless Voltage Data Loggers to record and monitor voltage for their critical applications in healthcare, health sciences, and research and manufacturing. These wireless data logger pods are specifically designed to hook up to 6 analog inputs, allowing an increase in the number … Continued
Reassociating an Accsense Wireless A1 Series Pod with a B1-06 Gateway
The popular Accsense wireless monitoring and alarming system operates on a public 2.4ghz wireless frequency. Since this is the same frequency used by many cordless phones, Wi-Fi systems, and various other wireless hardware systems, users can occasionally experience interference within this frequency band. When this type of interference occurs, there is a possibility that a … Continued
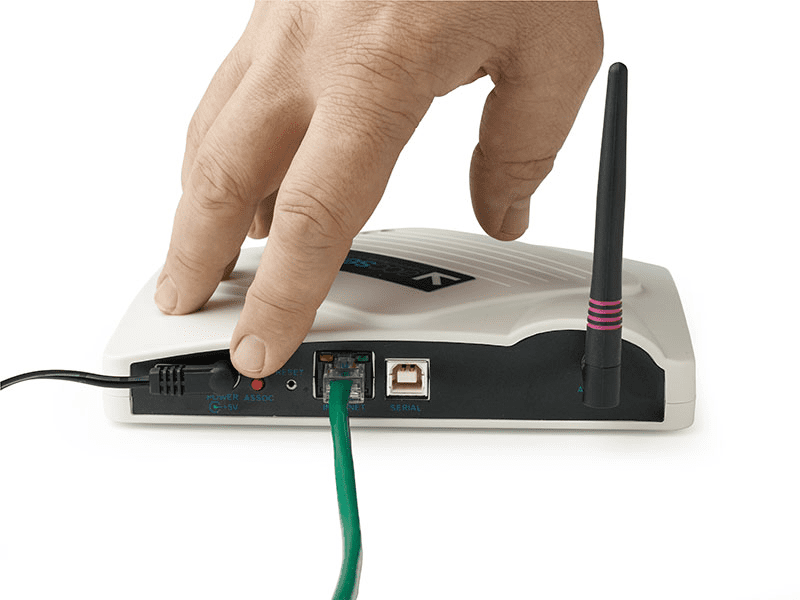
Troubleshooting the Accsense B1-06 Wireless Gateway
Diagnosing Network Connection Issues Network configuration errors can occasionally crop up when working with wireless monitoring systems. To help diagnose and remedy them, CAS DataLoggers presents this brief tutorial showing you how to troubleshoot network connection issues which may occur using the Accsense model B1-06 Wireless Gateway. We’ll cover two common failure modes, both of … Continued
Startup Process for the Accsense B1-06 Wireless Gateway
Cloud-Based Monitoring of Almost Any Parameter Gateway Startup Process: When users first connect an Accsense B1-06 wireless gateway to the network and power it up, it will go through the following process as it connects to the Acccsense server via the network: First the gateway will perform its Power On self-test. When this test is … Continued